Figure 2: Non-malicious file "obs-browser-page-exe" and "libcef.dll" along with the malicious "chrome_elf.dll."
Once executed, the Coyote banking Trojan keeps checking the title of the file or Internet browser window. Only when the window title matches one of the targets — mentioned below in the Targets section — does it start communication with its command-and-control (C2) servers.
Coyote can run a total of 24 commands and functions, including taking screenshots of a user’s activity, showing full-screen overlay windows (including an overlay of a fake banking app), making registry changes, moving the user’s mouse, machine shutdown and keylogging.
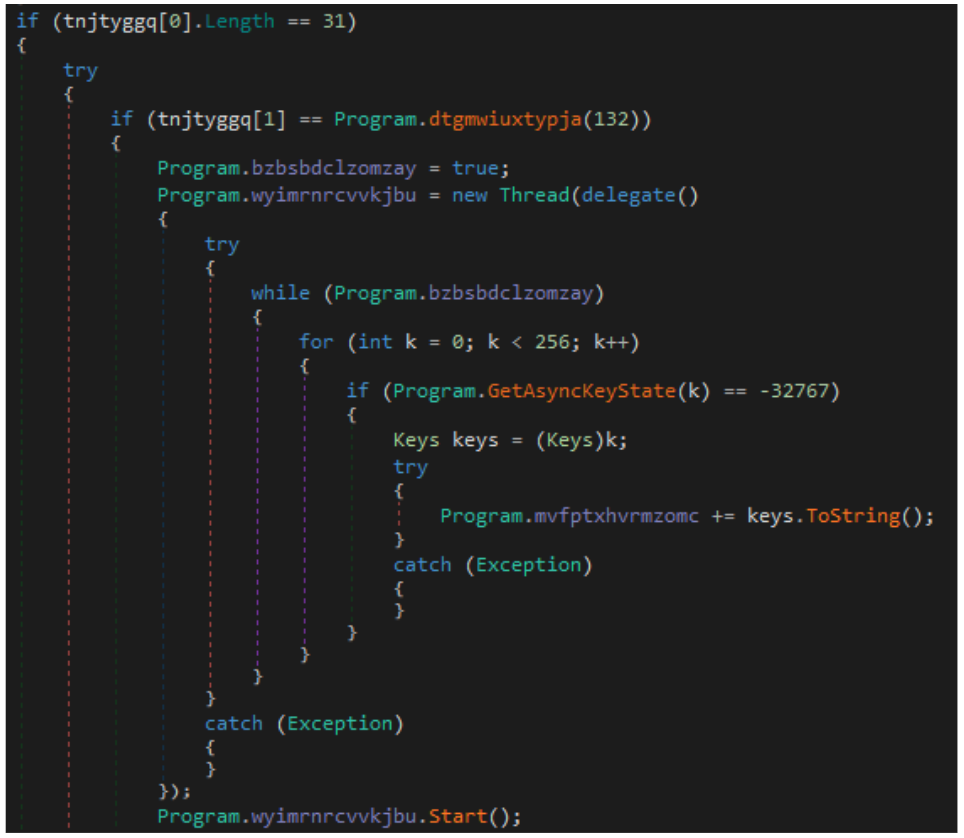
Figure 3: Coyote keylogger command.
Communication
Coyote uses the WatsonTCP library for communication. On the specific campaign we observed, the binary randomly selects one of the following C2s:
C2 |
bestoraculo[.]com |
acaodegraca[.]com |
turmadabruta[.]com |
britoingresso[.]com |
cinebrian[.]com |
Based on our analysis, we managed to find additional C2 servers besides those initially reported:
Additional C2s |
cloridatosys[.]com |
flogoral[.]com |
formitamina[.]com |
bilatex[.]com |
autoglobalcar[.]com |
atendesolucao[.]com |
angelcallcenter[.]com |
servicoasso[.]com |
dowfinanceiro[.]com |
centralsolucao[.]com |
gargamellojas[.]com |
marvelnatal[.]com |
nograusistema[.]com |
navegacaodura[.]com |
jogodequadra[.]com |
carrosantigo[.]com |
bermatechcliente[.]com |
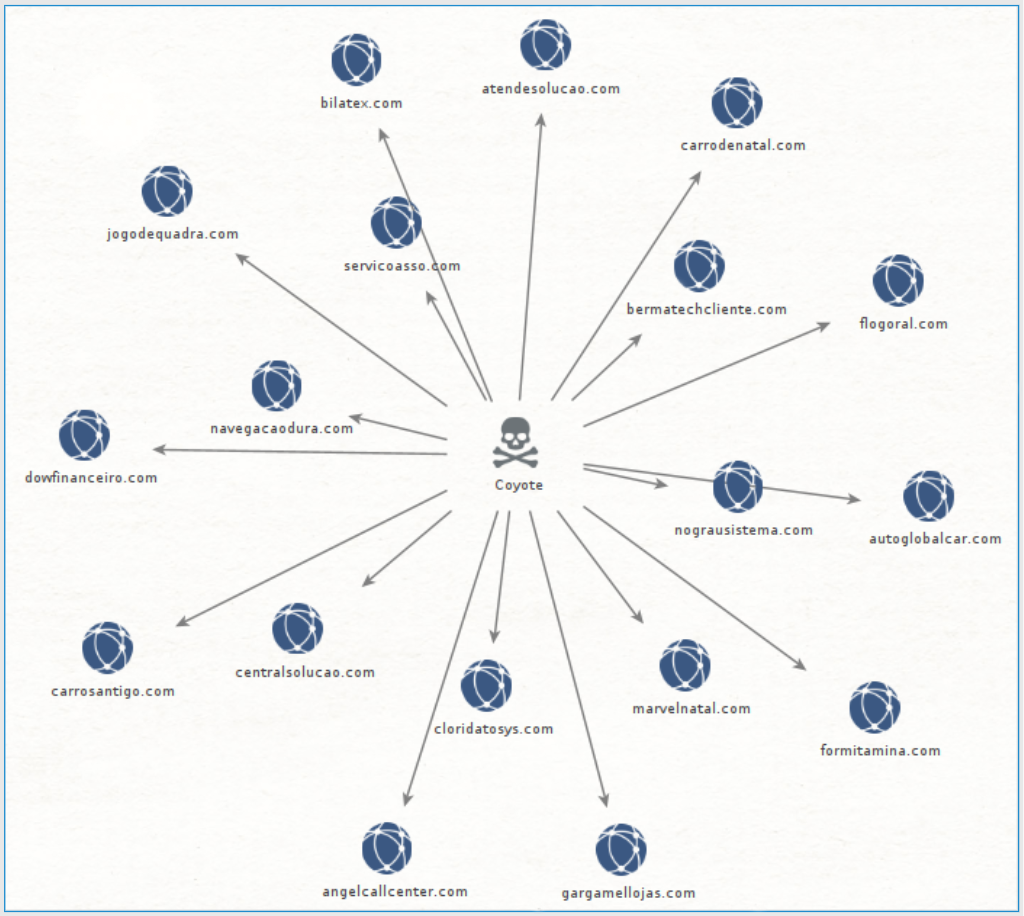
Figure 4: Connections from Coyote banking Trojan to different C2 servers.
With the different infection chain utilizing Squirrel and DLL side-loading targeting OBS, as well as a .NET Brazilian banking Trojan, we believe this is indeed the Coyote threat actor. At the time of writing this, there are no references to whether this specific banking Trojan is being sold on the underground market.
Targets
Coyote targets Brazilian financial institutions as well as Binance, a global company that operates a cryptocurrency exchange with the largest daily trading volume of cryptocurrencies. Coyote’s full target list of legitimate domains is as follows:
Targets (Legitimate Domains) |
Bancobrasil.com.br |
Bb.com.br |
internetbanking.caixa.gov.br |
loginx.caixa.gov.br |
banco.bradesco |
cidadetran.bradesco |
ne12.bradesconetempresa.b.br |
binance.com |
mercadobitcoin.com.br |
bitcointrade.com.br |
foxbit.com.br |
blockchain.com |
accounts.binance.com |
pf.santandernet.com.br |
pj.santandernetibe.com.br |
itau.com.br |
meu.original.com.br |
empresas.origina |
ibpj.original.com.br |
banrisul.com.br |
internetbanking.banpara.b.br |
ib.banpara.b.br |
www2s.bancoamazonia.com.br |
ecode.daycoval.com.br |
mercantildobrasi |
stone.com.br |
bancopan.com.br |
unicred.com.br |
safra.com.br |
safraempresas.com.br |
ib.brde.com.br |
banese.com.br |
bancobmg.com.br |
brbbanknet.brb.com.br |
internetbanking.confesol.com.br |
tribanco.com.br |
credisisbank.com.br |
credisan.com.br |
bancobs2.com.br |
bancofibra.com.br |
uniprimebr.com.br |
uniprime.com.br |
bancotopazio.com.br |
btgmais.com |
citidirect.com |
banestes.b.br |
zeitbank.com.br |
cora.com.br |
sofisa.com.br |
sofisadireto.com.br |
www.banestes.com.br |
banestes.com.br |
wwws.uniprimedobrasil.com.br |
www.rendimento.com.br |
rendimento.com.br |
contaonline.viacredi.coop.br |
sicredi.com.br |
nel.bnb.gov.br |
mercadopago.com.br |
Conclusion
The emergence of a .NET banking Trojan targeting the LATAM region with a primary focus on Brazil, underscores the rapid evolution of the cybersecurity threat landscape. This sophisticated malware employs unconventional methods to infiltrate targeted systems via phishing with malicious domains, with the goal of compromising large financial institutions.
The deceptive tactic of disguising the initial loader as a legitimate Squirrel update packager highlights the need for heightened vigilance and proactive security measures by defenders. As organizations fortify their cybersecurity defenses, it is crucial to not only invest in more advanced protective technologies, but to also prioritize user education. By enhancing employee awareness and understanding of threats such as these, we can significantly improve defensive evasion techniques and mitigate some of the risks.
Combating the Coyote banking Trojan threat head-on requires a multifaceted approach that integrates modern-day cybersecurity solutions with comprehensive user training. By staying ahead of emerging threats and fostering a culture of cyber resilience, we can safeguard our critical systems and protect the integrity of financial institutions in the LATAM region.
MITRE ATT&CK® Matrix
Tactic | Technique ID | Technique Name | Details |
Execution | T1059.007 | Command and Scripting Interpreter: JavaScript | Upon Squirrel execution, a NodeJS application runs and executes obfuscated JavaScript code. |
T1204.002 | User Execution: Malicious File | Initial loader is disguised as a Squirrel updater. | |
Persistence | T1547.001 | Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | Registry value is added into HKCU\Environment\UserInitMprLogonScript key (prior to checking its existence). The value added in the case we observed: “obs-browser-page.exe” is to establish persistence. |
Privilege Escalation | T1574.002 | Hijack Execution Flow: DLL Side-Loading | The Trojan is loaded through DLL side-loading of a dependency of Chrome and OBS Studio executables (libcef.dll). |
Defense Evasion | T1218 | System Binary Proxy Execution | Usage of Squirrel to create installation and updates packages hiding the infection vector in an updater. |
T1027 | Obfuscated Files or Information |
| |
T1620 | Reflective Code Loading | NIM is used to load the final stage, which unpacks the .NET executable and executes it in memory using the CLR. | |
T11036.001 | Masquerading: Match Legitimate Name or Location | Coyote hides its initial loader by presenting it as an update packager. | |
T1553.002 | Code Signing | Usage of signed application with legitimate library. | |
T1480.001 | Execution Guardrails | Once the malware verifies that the connection is indeed with the attacker, it proceeds to send the information collected from the infected machine and banking applications to the server. | |
Discovery | T1082 | System Information Discovery | Information sent to C2 includes:
|
T1010 | Application Windows Discovery | Trojan monitors all open applications on the victim’s system and waits for the specific banking application or website to be accessed. | |
Collection | T1056.001 | Input Capture: Keylogging | Trojan has the capability to conduct keylogging. |
T1113 | Screen Capture | Trojan has the capability to take screenshots. | |
Command and Control | T1573 | Encrypted Channel | Trojan establishes communication with its C2 server using SSL channels with a mutual authentication scheme. |
T1205 | Traffic Signaling | Attacker sends a response packet that contains specific actions. To process these actions, the attacker transmits a string with a random delimiter. Each position of the string is then converted to a list, with the first entry representing the command type. | |
Impact | T1529 | System Shutdown/Reboot | Trojan has capabilities to shut down the compromised system. |
Indicators of Compromise (IoCs):
SHA256 | File Type | Details |
096d7765f278bb0de33fbfa0a15413a2432060d09c99f15c6ca900a6a8a46365 9c6fc9e0854eaf5a0720caab1646f48c7992f6f4051438004598af89102a49eb e0b65087cc83b899d53c153fcfd1420d15e369c3d196325396b50cb75681c27d 485c8bfae3e5c150012e1d630f5d9ae37b786d4b750a9a0adf2b174b7ab85c65 16cc13258a3e63be247c9adf18def0369bb72197bdb3668142bc50a6656047af 2bd6bbe48d0328e4011ce3053e616664a4eb2bf43bd5762cb03be297f786b068 287b39f40ed541585c968b6529c44e9ccdd899bca0b88457907d994c2b5013f4 341a1945f606bcf4c25bce9b850dbddc5125376156cb7f8d14c6ce6bc4b396c3 9160ca25889427b2c2da4d4b14c4a93a707efc2ce07a49d5b8ab1a7f9be8ab55 2d8b10e35c2c2d9675ec693558629450eeee2c8e38f491d38c42de96bddf317a 112edf53d4c560ab71f1b20856ec4d6096e0ea42b0271526b3415c3563300f06 3cbc282c6a51edff4e762267332e1ff2a503f7ba8a7b2a10c9ff404a7bda913b aedffb9cf780bb52c68586ceb238fcaf90253524f06a4a338edc6437409e51c5 2b428df6f76d36ceeebfd37df65ab7893cb6f526afeb9e4494829628f0b9cae8 ae6676ad5b8ba386e88ae045eacc05225a657360963844cdf18db6a45318ea89 ce07ef596772e9cfa6f41000f27244f6f750527639a26c6be0b73033a8e41883 c0833babb2982e36ac7646f7539f6a235a42bcf5375bc080d3ac9d031dc3b903 d44f4db6680d178437e9cfba010ac049f80e5eddf43b3977da819119bb6ca06d 504a5902f20d0a7e3968251849cd88acd31e7fc895fc18d5c82076c5388df5bd 8e614368f99f955c75752df597f97de1dd51b4f0dfeeadc76e1badcc7ca57fc2 3cc58b46d0babd561508d7b67c609e0e9be9a35db9425f1e8a29512a5229665a 5656501522adfe1b08f58cccc1e187cbb7099ef1193a62edd5dfe0d32da4cd7a fb8353e718397dcabd11d9bd8a500ffd54e2a57ac4722a34241757c60ba2bdff ae65738fa81be0b2cfe2f63209db9ed5b928b4b5a1a703ce2a89699a6f192f07 5b3421beb6aaf3fd16831e1456475acac4f8e7c863869fb4d5dc9b1ae0576ef3 6b7a014d0674fe5f145aa2c5dc7674d42e5306d82c3fe7ab0235dcbfd559725f d96c3e8dc899948bf92c377bb4872b19b5983b6eb2d59f00019345293601843c 2a54b7f1327398ccd1c538759201e8699dfad7c53e8e095ea782d862ec48cb92 90ffb18c9d05bf6a61d90c57f299b70702c0e65dac90349b06d5e6833d6d2612 4869fcfda9be32f3cdd48c21bda07aefde496c5f06f235f33ce948169e9744e5 3edcf6a6b6cb254f72f0f2607fa4bb2ecb604475b448c9487e89fc76eb8f896e a0d2c87f4ed6522fdcd8c8d234dca9c7e8831de5faa9445275405ddd0a9104cc 6da5f450f3124e30e8091fda443cb416d29eab4e166a777263e004758acf2e69 10af5c8950b8802851afe96b423d20408b618f80ab54c1a5aef0f1a04c36f331 f6ed73bed9e6b992dbfdee64ff8c9dfde5e3f12c3ec6bbb4e2367fbd2ce75b6f 1ba49976a6e596abb68e2f7ca37407930330a4bf0bd25207057c5a60cb3a4107 798fb8de9bb0434ee0b172793f5b68eb593054538cf5ec96e71a5a0759f6bcc5 c057145da9481a4fff50e69b7e746c19cc95e2d33331539b6b62077169bc4b42 fcb8f32502147dbf8ef44ad99a41d9eaf639bb3d22c4de92a3022f501c9d8cb6 0dea05062d6527ab03f80de87488d278dd333167cdabdf5ef28da760bf252863 3a14ab878697453832306a836e67915d7475481307c65268ceb1f900ff4ec25a | ZIP
| Malware Delivery
|
eb615c093e9b52ed409f426764857e6e42aa85e02adef59d6f1457dcbb90bb40 1bed3755276abd9b54db13882fcf29c543ebf604be3b7fcf060cbd6d68bcd23f 4806617bbc8187a89d5ed73cb818853e306d3699f87bd09940b0ecffdc96091d 1d59bc782e532780da0364b14a1b474a8cb8a5af50c8124159bf5d943bd050f7 | DLL | NIM Loader + Coyote banking Trojan
|
IP/Domain | Details |
cloridatosys[.]com flogoral[.]com formitamina[.]com bilatex[.]com autoglobalcar[.]com atendesolucao[.]com angelcallcenter[.]com servicoasso[.]com dowfinanceiro[.]com centralsolucao[.]com gargamellojas[.]com carrodenatal[.]com marvelnatal[.]com nograusistema[.]com navegacaodura[.]com jogodequadra[.]com carrosantigo[.]com bermatechcliente[.]com | Recently active malicious Coyote C2’s |
Countermeasures
The good news is that BlackBerry customers are protected against the Coyote IoCs listed in this blog post by endpoint protection solutions such as CylanceENDPOINT™. CylanceENDPOINT leverages advanced AI to detect threats before they cause damage, minimizing business disruptions and the costs incurred during a ransomware attack.
YARA Rule
import "pe" rule coyote_nimloader { |
Further Reading:
- Threat Analysis Insight: RisePro Information Stealer
- Transparent Tribe Targets Indian Government, Defense, and Aerospace Sectors Leveraging Cross-Platform Programming Languages
- LightSpy Returns: Renewed Espionage Campaign Targets Southern Asia, Possibly India
- Threat Group FIN7 Targets the U.S. Automotive Industry


No comments:
Post a Comment